Unlock Ok theo solu trên :D
C:\adb>adb push run_root_shell /data/local/tmp/
3251 KB/s (89892 bytes in 0.027s)
C:\adb>adb shell chmod 755 /data/local/tmp/run_root_shell
C:\adb>adb push revone-0.2 //data/local/tmp/
4248 KB/s (648208 bytes in 0.149s)
C:\adb>adb shell
shell[MENTION=436806]Android[/MENTION]:/ $ cd /data/local/tmp
cd /data/local/tmp
shell[MENTION=436806]Android[/MENTION]:/data/local/tmp $ ./run_root_shell
./run_root_shell
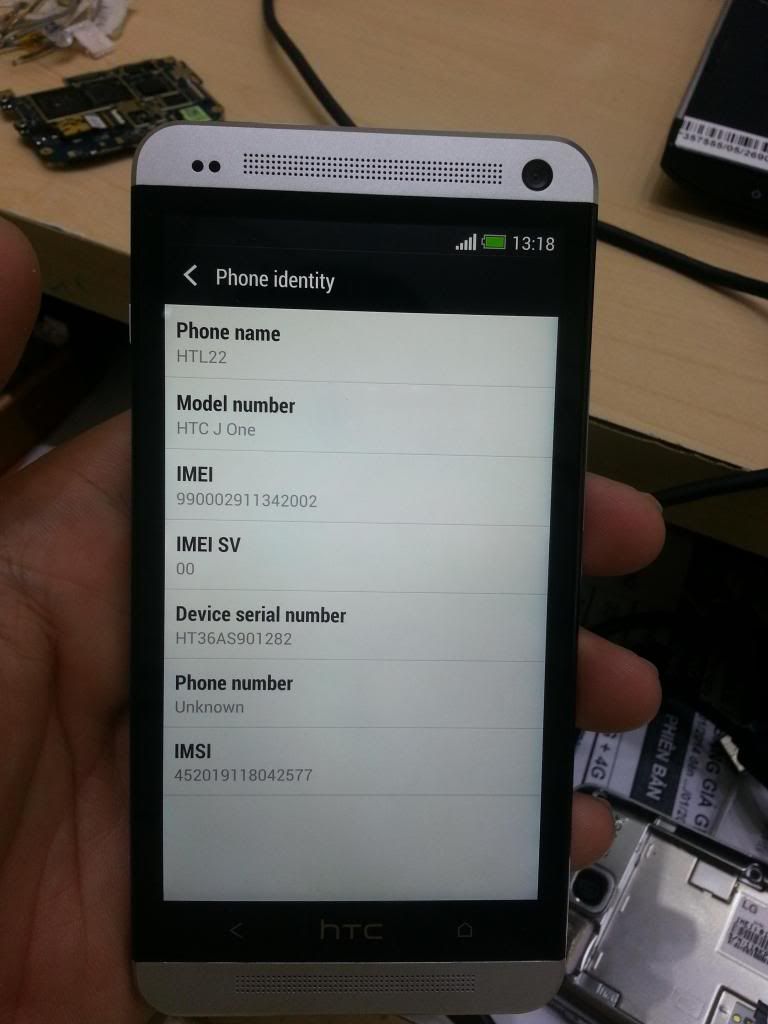
Device detected: HTL22 (JZO54K)
Attempt acdb exploit...
HTL22 (JZO54K 1.05.970.2) is not supported.
Attempt fj_hdcp exploit...
Attempt msm_cameraconfig exploit...
Detected kernel physical address at 0x80608000 form iomem
Attempt fb_mem exploit...
Detected kernel physical address at 0x80608000 form iomem
shell[MENTION=436806]Android[/MENTION]:/data/local/tmp # ./revone-0.2.1-wlj -P
./revone-0.2.1-wlj -P
revone v0.2.1
revone successful - no need to reboot.
10|shell[MENTION=436806]Android[/MENTION]:/data/local/tmp # reboot
reboot
C:\adb>adb shell
shell[MENTION=436806]Android[/MENTION]:/ $ cd /data/local/tmp
cd /data/local/tmp
shell[MENTION=436806]Android[/MENTION]:/data/local/tmp $ ./run_root_shell
./run_root_shell
Device detected: HTL22 (JZO54K)
Attempt acdb exploit...
HTL22 (JZO54K 1.05.970.2) is not supported.
Attempt fj_hdcp exploit...
Attempt msm_cameraconfig exploit...
Detected kernel physical address at 0x80608000 form iomem
Attempt fb_mem exploit...
Detected kernel physical address at 0x80608000 form iomem
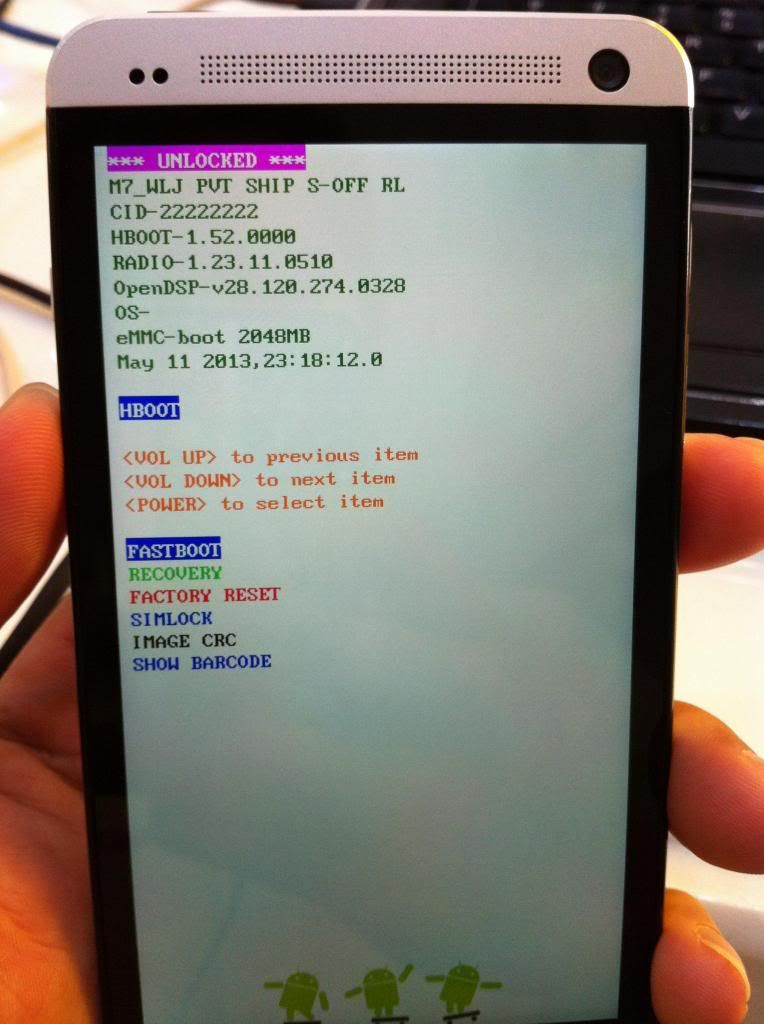
shell[MENTION=436806]Android[/MENTION]:/data/local/tmp # ./revone-0.2.1-wlj -s 0 -l -t
./revone-0.2.1-wlj -s 0 -l -t
revone v0.2.1
revone successful.
shell[MENTION=436806]Android[/MENTION]:/data/local/tmp # reboot bootloader
reboot bootloader
C:\adb>fastboot oem get_identifier_token
...
(bootloader)
(bootloader) < Please cut following message >
(bootloader) <<<< Identifier Token Start >>>>
(bootloader) 8CD528DA404E15D3C9DA2C6D95DCE69C
(bootloader) 7682279CD2BFAF43770831C727CBF5D9
(bootloader) BC8850B6123B0FE39DE026A368B70B6E
(bootloader) 4541482434A088E91C01A1E940E39D4F
(bootloader) 1CED1A426F5395C37E118CBA83DE9CFB
(bootloader) 324F9834DA078B52D1FA202BC26BECCF
(bootloader) 7A6BA10F70731C3D1A02D48F322C09A6
(bootloader) F04BD4C503CE3D1C7534C281C2315D98
(bootloader) 703670EB797310B517C05DE3964A2265
(bootloader) 187D7D47C07AFF84FFD96A5FA25ADBBF
(bootloader) EB45EA54775BDC63DE7A7AD7ED29BBA0
(bootloader) 2B6AB97F5DA9380B9984F941046D1D93
(bootloader) 9579F6D9F26A7705160CAF10F808E11C
(bootloader) DCDDBD23383DAA5D3C826C357049711F
(bootloader) B3742982CD43FA723A53A705430F1FF5
(bootloader) C4CC86A833533AE93BDBF5F568027B7A
(bootloader) <<<<< Identifier Token End >>>>>
OKAY [ 0.069s]
finished. total time: 0.070s
C:\adb>fastboot oem writecid 11111111
...
(bootloader) Start Verify: 0
OKAY [ 0.027s]
finished. total time: 0.028s
C:\adb>fastboot flash recovery "D:\Dien_Thoai\Android\HTC\HTC ONE\HTC ONE J HTL2
2\twrp250-m7_wlj.img"
sending 'recovery' (8018 KB)...
OKAY [ 1.078s]
writing 'recovery'...
OKAY [ 0.819s]
finished. total time: 1.899s
C:\adb>fastboot boot "D:\Dien_Thoai\Android\HTC\HTC ONE\HTC ONE J HTL22\twrp250-
m7_wlj.img"
downloading 'boot.img'...
OKAY [ 1.077s]
booting...
OKAY [ 0.002s]
finished. total time: 1.080s